Internet-of-Things
Systems in the Internet-of-Things (IoT) typically have a long operating time, limited processing resources and a reduced battery life. In the process, they may also incur only low costs in production and operation. Due to these constraints, many of the established security technologies cannot be directly transferred to the IoT domain. One research focus of the department Hardware Security therefore lies on innovative hardware and software design patterns that aim to increase the resilience of IoT devices with limited resources against cyber attacks. These include, for example, memory protection mechanisms, system attestation and identities, and measures against denial-of-service attacks.
Medical Devices
Connected medical devices and so-called wearables, such as continuous glucose monitors or implanted pacemakers, are exposed to high risks of attack due to their increasing distribution and functionality. Based on our analysis and solution expertise from hardware to networks security, we help manufacturers to design secure devices that also meet the requirements of the new Medical Device Regulation (MDR).
Sensor Networks
Wireless sensor networks are the sensory organs of the Internet-of-Things. Often, the collected data is critical and must be protected against eavesdropping or manipulation. The management of the cryptographic keys required for this purpose is challenging due to the large number of sensor nodes and their limited computing power. We are therefore continuously expanding our expertise in the field of key management solutions that combine security and user-friendliness and enable any user to easily operate secure wireless sensor networks.
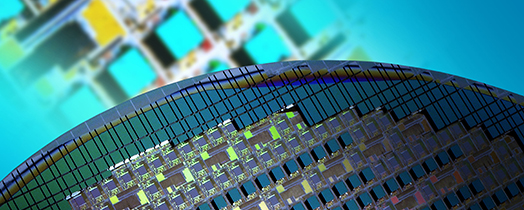
System-on-Chips
Systems-on-chips (SoCs) combine a multitude of functions in a single chip. They are the foundation of countless embedded systems and must therefore be protected carefully. The many functions of an SoC provide a large surface for attack, which makes securing them a major challenge. Debug interfaces and external memory modules must be secured, cryptographic keys must be stored in a secure manner, and software must be executed securely. Secure boot and update, firmware encryption, key storage, protection of intellectual property and secure execution environments are just some of the topics that have been the focus of the Hardware Security department for years.
Tamper Protection
Embedded systems are exposed to physical tampering to manipulate the system or derive critical secrets, especially in the domain of high-assurance communication. Detecting and reacting to tampering requires the interaction of sensor technologies, electronics and embedded security. We are collaborating with technology partners to design new tamper protection methods, in particular based on Physical Unclonable Function (PUFs) to assess the physical integrity of a device based on the validity of a physical hardware fingerprint.
 Fraunhofer Institute for Applied and Integrated Security
Fraunhofer Institute for Applied and Integrated Security